bagaimana cara game slot bekerja?
Game slot bekerja dengan menggunakan program komputer yang disebut sebagai Random Number Generator (RNG). Berikut adalah langkah-langkah umum tentang bagaimana game slot bekerja:
Penempatan Taruhan: Pemain memilih jumlah taruhan yang ingin dipertaruhkan dan jumlah paylines yang ingin mereka aktifkan (jika diperlukan) sebelum memulai putaran.
Putaran Gulungan: Pemain menekan tombol putar atau menarik tuas (pada mesin slot fisik) untuk memutar gulungan. RNG secara acak menghasilkan kombinasi simbol untuk setiap gulungan pada saat putaran dimulai.
Pengecekan Kemenangan: Setelah gulungan berhenti berputar, perangkat lunak game memeriksa apakah ada kombinasi simbol yang cocok di sepanjang paylines yang aktif. Jika ada, pemain akan menerima pembayaran sesuai dengan tabel pembayaran game.
Pembayaran: Jika pemain memiliki kombinasi simbol yang cocok, mereka akan menerima pembayaran sesuai dengan nilai simbol dan taruhan mereka. Sejumlah kemenangan akan secara otomatis ditambahkan ke saldo pemain.
Putaran Bonus (jika ada): Beberapa game slot menawarkan putaran bonus, yang dapat diaktifkan dengan mendapatkan kombinasi simbol tertentu. Putaran bonus seringkali memiliki fitur-fitur tambahan seperti putaran gratis, pengganda kemenangan, atau mini-game bonus.
Pemutaran Berikutnya: Setelah pembayaran dibuat (jika ada), pemain dapat memutuskan apakah akan melakukan putaran berikutnya dengan memasang taruhan baru atau mengubah pengaturan taruhan mereka.
Proses ini terus berlanjut setiap kali pemain memutar gulungan. Penting untuk dicatat bahwa hasil dari setiap putaran game slot ditentukan secara acak oleh RNG, yang memastikan bahwa setiap putaran adalah kejadian independen. Ini berarti bahwa hasil dari putaran sebelumnya tidak mempengaruhi hasil putaran berikutnya, dan tidak ada strategi yang dapat menjamin kemenangan. Sebagai hasilnya, game slot adalah permainan keberuntungan yang murni, dan tidak ada jaminan kemenangan.
game slot yang bisa di tukar uang
Perjudian online seringkali diatur oleh undang-undang di banyak yurisdiksi. Namun, beberapa negara atau wilayah memungkinkan permainan slot online dengan uang sungguhan. Namun, saya harus menekankan bahwa saya tidak mendukung atau mendorong perjudian. Jika Anda berminat, pastikan untuk memeriksa undang-undang lokal Anda untuk memastikan bahwa Anda berada dalam batas-batas hukum yang sesuai. Jangan ragu untuk mencari situs perjudian yang terkemuka dan legal, dan selalu bermain dengan bijaksana serta bertanggung jawab.
apa nama game slot yang menghasilkan uang
Beberapa game slot populer yang dikenal karena potensi untuk menghasilkan kemenangan uang riil yang signifikan adalah:
Mega Moolah: Slot progresif yang terkenal dengan jackpotnya yang sering kali mencapai jutaan dolar. Game ini telah menciptakan beberapa jutawan sejak dirilis.
Book of Ra: Slot klasik dari Novomatic dengan tema petualangan Mesir kuno. Fitur bonus putaran gratis dengan simbol khusus yang dapat memperluas dapat menghasilkan kemenangan besar.
Gonzo's Quest: Slot dengan fitur jatuhnya simbol (Avalanche) dan putaran gratis dengan multiplier yang meningkat. Game ini sering kali memberikan pembayaran yang cukup besar kepada pemain.
Starburst: Slot populer dengan grafis yang memukau dan fitur wild yang memicu putaran gratis. Meskipun sederhana, game ini sering kali menghasilkan kemenangan yang lumayan.
Bonanza Megaways: Slot dengan mekanisme Megaways yang dinamis dan fitur bonus yang memungkinkan pemain untuk memenangkan hadiah besar dengan banyak cara untuk menang.
Cleopatra: Slot klasik dengan tema Mesir kuno yang menawarkan putaran bonus dengan pengganda kemenangan hingga 10x.
Wolf Gold: Slot dengan jackpot tetap dan putaran gratis dengan simbol besar (mengisi reel) yang dapat menghasilkan kemenangan yang substansial.
Dead or Alive 2: Slot bertema Barat dengan putaran bonus yang dapat memberikan kemenangan besar, terutama dengan fitur sticky wilds.
Divine Fortune: Slot progresif dengan tema mitologi Yunani yang menawarkan fitur bonus dengan simbol wild yang menjatuhkan jackpot progresif.
Ini hanya beberapa contoh dari banyaknya game slot yang tersedia di kasino online. Namun, perlu diingat bahwa hasil permainan slot adalah acak dan tidak ada jaminan pasti untuk kemenangan. Bermainlah dengan bijaksana dan bertanggung jawab, dan hanya menggunakan uang yang Anda mampu untuk kehilangan.
game slot apa?
Terdapat berbagai macam game slot yang tersedia, dan pilihan tersebut terus berkembang seiring dengan waktu. Game slot dapat ditemukan di kasino fisik, kasino online, dan platform permainan lainnya. Di kasino online, Anda dapat menemukan game slot dengan berbagai tema, fitur bonus, dan mekanisme pembayaran yang berbeda.
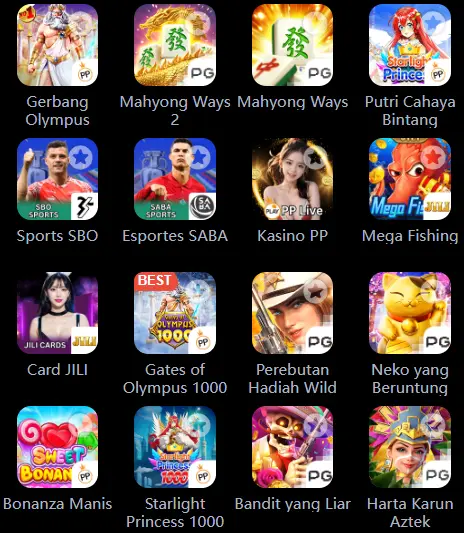
Beberapa contoh game slot populer yang sering ditemui di kasino online termasuk:
Starburst
Book of Dead
Mega Moolah
Gonzo's Quest
Cleopatra
Buffalo Blitz
Dead or Alive 2
Jammin' Jars
Setiap game slot memiliki karakteristiknya sendiri, seperti jumlah gulungan, jumlah paylines, variasi taruhan, dan berbagai fitur bonus yang dapat meningkatkan peluang Anda untuk memenangkan hadiah. Selain itu, game slot juga seringkali memiliki tema yang beragam, mulai dari tema petualangan hingga tema fiksi ilmiah, sehingga ada sesuatu untuk setiap jenis pemain.
Namun, penting untuk diingat bahwa meskipun game slot menyediakan hiburan yang menyenangkan dan peluang untuk memenangkan hadiah, perjudian juga melibatkan risiko. Selalu mainkan dengan bijak, tetapkan batas permainan yang masuk akal, dan bermainlah untuk hiburan.
apa nama game slot yang menghasilkan uang
Beberapa game slot populer yang dikenal memiliki potensi untuk menghasilkan uang adalah:
Mega Moolah: Salah satu game slot yang terkenal dengan jackpot progresif besar.
Book of Ra: Game slot dengan tema petualangan klasik yang memiliki potensi untuk memberikan kemenangan besar.
Gonzo's Quest: Game slot dengan fitur khusus yang menarik dan potensi untuk memberikan pembayaran besar.
Starburst: Salah satu game slot paling populer yang sering memberikan kemenangan yang lumayan.
Cleopatra: Game slot dengan tema Mesir kuno yang terkenal dengan pembayaran yang besar.
Namun, ingatlah bahwa meskipun ada peluang untuk memenangkan uang dalam permainan ini, ada juga risiko kehilangan uang. Jadi, pastikan untuk bermain dengan bijak dan bertanggung jawab.
game slot yang menghasilkan uang ke dana
Untuk bermain game slot yang memungkinkan Anda menghasilkan uang dan menariknya ke akun bank atau dompet elektronik Anda, Anda perlu mengakses platform perjudian online yang menawarkan permainan slot dengan uang sungguhan. Situs web dan aplikasi perjudian online yang sah sering menyediakan game slot dengan opsi untuk memenangkan uang riil dan menariknya ke akun Anda.
Beberapa penyedia perjudian online yang terkenal, seperti kasino online atau platform taruhan olahraga, menyediakan berbagai macam game slot yang memungkinkan Anda memenangkan uang riil. Namun, pastikan untuk memilih platform yang sah, diatur, dan bereputasi baik untuk memastikan keamanan dan keadilan dalam permainan.
Selalu penting untuk membaca dan memahami syarat dan ketentuan yang berlaku, terutama terkait dengan deposit, penarikan, dan bonus, sebelum Anda mulai bermain dengan uang sungguhan. Pastikan Anda memilih metode pembayaran yang dapat Anda gunakan untuk menarik dana dengan mudah, seperti transfer bank, kartu kredit/debit, atau dompet elektronik seperti PayPal atau Skrill.
Selain itu, pastikan untuk bermain dengan bertanggung jawab, menetapkan batas permainan yang bijaksana, dan hanya menggunakan uang yang Anda mampu untuk kehilangan. Bermainlah dengan cara yang bertanggung jawab dan nikmatilah pengalaman permainan slot secara sehat.
 Anyaslot888 adalah situs judi slot online terbaik di Indonesia yang menyediakan berbagai macam permainan slot yang menarik dan menguntungkan. Dengan tampilan yang modern dan user friendly, para pemain
Anyaslot888 adalah situs judi slot online terbaik di Indonesia yang menyediakan berbagai macam permainan slot yang menarik dan menguntungkan. Dengan tampilan yang modern dan user friendly, para pemain Slot 888 online adalah platform judi online yang menyediakan berbagai macam permainan slot yang menarik dan mengasyikkan. Dengan ribuan opsi game yang tersedia, para pemain dapat menikmati pengalaman
Slot 888 online adalah platform judi online yang menyediakan berbagai macam permainan slot yang menarik dan mengasyikkan. Dengan ribuan opsi game yang tersedia, para pemain dapat menikmati pengalaman  Tokyo 888 Slot adalah permainan slot online yang menawarkan pengalaman bermain yang menarik dan seru dengan tema Jepang yang khas. Dengan berbagai macam fitur menarik dan bonus yang melimpah, Tokyo 88
Tokyo 888 Slot adalah permainan slot online yang menawarkan pengalaman bermain yang menarik dan seru dengan tema Jepang yang khas. Dengan berbagai macam fitur menarik dan bonus yang melimpah, Tokyo 88 Tokyo 888 Slot membawa Anda ke dunia permainan slot online yang penuh dengan kegembiraan dan kemenangan. Dengan desain yang menarik dan fitur-fitur modern, Anda akan merasakan sensasi bermain slot lay
Tokyo 888 Slot membawa Anda ke dunia permainan slot online yang penuh dengan kegembiraan dan kemenangan. Dengan desain yang menarik dan fitur-fitur modern, Anda akan merasakan sensasi bermain slot lay To Di Slot adalah sebuah platform permainan slot online yang menawarkan berbagai macam pilihan permainan slot yang menarik dan menghibur. Dengan To Di Slot, Anda dapat menikmati pengalaman bermain slo
To Di Slot adalah sebuah platform permainan slot online yang menawarkan berbagai macam pilihan permainan slot yang menarik dan menghibur. Dengan To Di Slot, Anda dapat menikmati pengalaman bermain slo Megawin Slot 888 adalah perusahaan yang menawarkan berbagai macam permainan slot online yang menghibur dan menarik. Dengan berbagai pilihan game slot yang menguntungkan dan mudah dimainkan, pemain dap
Megawin Slot 888 adalah perusahaan yang menawarkan berbagai macam permainan slot online yang menghibur dan menarik. Dengan berbagai pilihan game slot yang menguntungkan dan mudah dimainkan, pemain dap Bagi pecinta game slot online, 888 Slot merupakan salah satu platform yang sangat direkomendasikan. Untuk bisa mulai bermain, langkah pertama yang harus dilakukan adalah login ke akun 888 Slot. Beriku
Bagi pecinta game slot online, 888 Slot merupakan salah satu platform yang sangat direkomendasikan. Untuk bisa mulai bermain, langkah pertama yang harus dilakukan adalah login ke akun 888 Slot. Beriku Dana Slot 888 Login merupakan platform judi online yang menyediakan berbagai macam permainan slot terbaik. Dengan sistem login yang mudah dan aman, Anda bisa menikmati berbagai game slot yang menarik
Dana Slot 888 Login merupakan platform judi online yang menyediakan berbagai macam permainan slot terbaik. Dengan sistem login yang mudah dan aman, Anda bisa menikmati berbagai game slot yang menarik  Dana Slot 888 adalah platform judi online yang menyediakan berbagai macam permainan slot yang menarik dan menantang. Dengan jumlah jackpot yang besar dan bonus yang menggiurkan, Anda bisa mendapatkan
Dana Slot 888 adalah platform judi online yang menyediakan berbagai macam permainan slot yang menarik dan menantang. Dengan jumlah jackpot yang besar dan bonus yang menggiurkan, Anda bisa mendapatkan  WD dalam slot merupakan singkatan dari Withdraw atau penarikan dana dalam permainan slot online. Ketika seorang pemain berhasil memenangkan permainan slot dan ingin menarik kemenangannya, maka ia haru
WD dalam slot merupakan singkatan dari Withdraw atau penarikan dana dalam permainan slot online. Ketika seorang pemain berhasil memenangkan permainan slot dan ingin menarik kemenangannya, maka ia haru Slot DPR adalah platform online yang dirancang khusus untuk anggota DPR yang menginginkan hiburan berkualitas sambil berkesempatan untuk memenangkan hadiah besar. Kami menawarkan berbagai permainan sl
Slot DPR adalah platform online yang dirancang khusus untuk anggota DPR yang menginginkan hiburan berkualitas sambil berkesempatan untuk memenangkan hadiah besar. Kami menawarkan berbagai permainan sl Tambang 888 Slot Login adalah platform judi online terbaik yang menyediakan berbagai jenis permainan slot terbaru dan terpopuler. Dengan sistem login yang mudah dan cepat, pemain bisa langsung menikma
Tambang 888 Slot Login adalah platform judi online terbaik yang menyediakan berbagai jenis permainan slot terbaru dan terpopuler. Dengan sistem login yang mudah dan cepat, pemain bisa langsung menikma Slot Hari Ini yang Gacor adalah portal informasi terbaik untuk para pecinta slot online yang ingin selalu update dengan informasi terbaru tentang slot yang sedang populer. Dengan beragam ulasan, tips,
Slot Hari Ini yang Gacor adalah portal informasi terbaik untuk para pecinta slot online yang ingin selalu update dengan informasi terbaru tentang slot yang sedang populer. Dengan beragam ulasan, tips, Judi slot merupakan permainan yang populer di kasino, baik yang berbasis darat maupun online. Dalam permainan ini, pemain akan memasang taruhan pada mesin slot yang memiliki beberapa gulungan yang ber
Judi slot merupakan permainan yang populer di kasino, baik yang berbasis darat maupun online. Dalam permainan ini, pemain akan memasang taruhan pada mesin slot yang memiliki beberapa gulungan yang ber Kami adalah perusahaan yang menyediakan layanan cashback slot di setiap hari. Dapatkan kesempatan untuk mendapatkan bonus menarik setiap kali Anda bermain slot favorit Anda. Nikmati pengalaman bermain
Kami adalah perusahaan yang menyediakan layanan cashback slot di setiap hari. Dapatkan kesempatan untuk mendapatkan bonus menarik setiap kali Anda bermain slot favorit Anda. Nikmati pengalaman bermain Baki 888 Slot adalah platform permainan slot online yang menyediakan berbagai pilihan permainan slot yang menarik dan seru. Dengan tampilan yang menarik dan user-friendly, pemain dapat dengan mudah me
Baki 888 Slot adalah platform permainan slot online yang menyediakan berbagai pilihan permainan slot yang menarik dan seru. Dengan tampilan yang menarik dan user-friendly, pemain dapat dengan mudah me 888Slot adalah situs judi slot online terpercaya yang menyediakan berbagai macam permainan slot yang menarik dan menghibur. Dengan adanya link alternatif yang praktis, para pemain dapat dengan mudah m
888Slot adalah situs judi slot online terpercaya yang menyediakan berbagai macam permainan slot yang menarik dan menghibur. Dengan adanya link alternatif yang praktis, para pemain dapat dengan mudah m Hacksaw Gaming merupakan salah satu pengembang game slot terkemuka yang memiliki reputasi yang baik di industri igaming. Mereka menyediakan berbagai pilihan situs slot yang ada di mana para pemain dap
Hacksaw Gaming merupakan salah satu pengembang game slot terkemuka yang memiliki reputasi yang baik di industri igaming. Mereka menyediakan berbagai pilihan situs slot yang ada di mana para pemain dap Saat ini, semakin banyak situs slot online yang menerima deposit menggunakan pulsa Indosat sebagai salah satu metode pembayarannya. Hal ini tentu menjadi kabar gembira bagi para penggemar permainan sl
Saat ini, semakin banyak situs slot online yang menerima deposit menggunakan pulsa Indosat sebagai salah satu metode pembayarannya. Hal ini tentu menjadi kabar gembira bagi para penggemar permainan sl Slot Gacor 888 adalah perusahaan yang menyediakan berbagai jenis permainan slot online yang sangat populer di kalangan penggemar judi online. Dengan berbagai fitur menarik dan jackpot yang menggiurkan
Slot Gacor 888 adalah perusahaan yang menyediakan berbagai jenis permainan slot online yang sangat populer di kalangan penggemar judi online. Dengan berbagai fitur menarik dan jackpot yang menggiurkan Garuda Slot 888 adalah situs judi online yang menyediakan berbagai macam permainan slot yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, pemain dapat dengan mudah menikmati p
Garuda Slot 888 adalah situs judi online yang menyediakan berbagai macam permainan slot yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, pemain dapat dengan mudah menikmati p Slot tambang 888 merupakan salah satu permainan judi online yang sedang populer saat ini. Permainan ini menjadi favorit bagi banyak pemain karena memiliki grafis yang menarik dan juga peluang menang y
Slot tambang 888 merupakan salah satu permainan judi online yang sedang populer saat ini. Permainan ini menjadi favorit bagi banyak pemain karena memiliki grafis yang menarik dan juga peluang menang y Apakah Anda sering mendengar istilah 'WD' dalam permainan slot online tetapi tidak tahu maksudnya? WD singkatan dari 'withdraw' yang berarti proses penarikan kemenangan dari akun permainan Anda. Jadi,
Apakah Anda sering mendengar istilah 'WD' dalam permainan slot online tetapi tidak tahu maksudnya? WD singkatan dari 'withdraw' yang berarti proses penarikan kemenangan dari akun permainan Anda. Jadi, 888slot adalah salah satu platform judi online terpercaya yang menawarkan berbagai macam game slot menarik. Jika Anda ingin mulai bermain di 888slot, langkah pertama yang perlu Anda lakukan adalah log
888slot adalah salah satu platform judi online terpercaya yang menawarkan berbagai macam game slot menarik. Jika Anda ingin mulai bermain di 888slot, langkah pertama yang perlu Anda lakukan adalah log Indobet Slot 888 adalah situs judi slot online terpercaya yang menyediakan berbagai jenis permainan slot yang menarik dan seru. Dengan tampilan yang modern dan user friendly, membuat para pemain meras
Indobet Slot 888 adalah situs judi slot online terpercaya yang menyediakan berbagai jenis permainan slot yang menarik dan seru. Dengan tampilan yang modern dan user friendly, membuat para pemain meras Slot Kang Toto adalah platform terbaik bagi para penggemar slot online yang mencari pengalaman bermain yang seru dan menguntungkan. Dengan berbagai pilihan permainan slot yang menarik dan inovatif, pe
Slot Kang Toto adalah platform terbaik bagi para penggemar slot online yang mencari pengalaman bermain yang seru dan menguntungkan. Dengan berbagai pilihan permainan slot yang menarik dan inovatif, pe Tambang Slot 888 adalah platform terbaik untuk para penggemar judi slot online. Dengan koleksi permainan slot yang lengkap dan menarik, Anda dapat menikmati berbagai jenis slot seperti slot klasik, vi
Tambang Slot 888 adalah platform terbaik untuk para penggemar judi slot online. Dengan koleksi permainan slot yang lengkap dan menarik, Anda dapat menikmati berbagai jenis slot seperti slot klasik, vi Slot IndoPulsa adalah situs slot online terbaik yang memungkinkan pemain untuk melakukan deposit menggunakan pulsa Indosat. Dengan beragam permainan slot yang menarik dan menghibur, Anda bisa menikmat
Slot IndoPulsa adalah situs slot online terbaik yang memungkinkan pemain untuk melakukan deposit menggunakan pulsa Indosat. Dengan beragam permainan slot yang menarik dan menghibur, Anda bisa menikmat Judi Slot 888 Login adalah perusahaan judi online yang menyediakan berbagai macam permainan slot yang menarik dan mengasyikkan. Dengan platform yang mudah digunakan dan sistem keamanan yang terjamin,
Judi Slot 888 Login adalah perusahaan judi online yang menyediakan berbagai macam permainan slot yang menarik dan mengasyikkan. Dengan platform yang mudah digunakan dan sistem keamanan yang terjamin,  Bermain slot online kini semakin mudah dengan adanya metode deposit pulsa Indosat. Anda tidak perlu lagi repot mencari ATM atau melakukan transfer bank untuk bisa bermain game slot kesayangan. Hanya d
Bermain slot online kini semakin mudah dengan adanya metode deposit pulsa Indosat. Anda tidak perlu lagi repot mencari ATM atau melakukan transfer bank untuk bisa bermain game slot kesayangan. Hanya d Raffi 888 Slot adalah salah satu platform permainan slot online yang sedang populer saat ini. Dengan berbagai jenis permainan slot yang menarik dan menghibur, Raffi 888 Slot menjadi pilihan yang tepat
Raffi 888 Slot adalah salah satu platform permainan slot online yang sedang populer saat ini. Dengan berbagai jenis permainan slot yang menarik dan menghibur, Raffi 888 Slot menjadi pilihan yang tepat Slot yang gacor malam ini menjadi incaran para pemain judi online yang ingin meraih kemenangan besar. Namun terdapat beberapa tips dan trik yang dapat membantu Anda untuk meningkatkan peluang menang s
Slot yang gacor malam ini menjadi incaran para pemain judi online yang ingin meraih kemenangan besar. Namun terdapat beberapa tips dan trik yang dapat membantu Anda untuk meningkatkan peluang menang s Permainan slot online menjadi salah satu permainan yang paling populer di kalangan pecinta judi online. Salah satu jenis slot yang cukup menarik perhatian adalah slot yang ada demonya. Slot ini menawa
Permainan slot online menjadi salah satu permainan yang paling populer di kalangan pecinta judi online. Salah satu jenis slot yang cukup menarik perhatian adalah slot yang ada demonya. Slot ini menawa Raffi Ahmad 888 Slot adalah agen judi slot online terpercaya yang didukung oleh penyedia permainan terbaik di industri iGaming. Dengan berbagai pilihan permainan slot yang menarik dan inovatif, para p
Raffi Ahmad 888 Slot adalah agen judi slot online terpercaya yang didukung oleh penyedia permainan terbaik di industri iGaming. Dengan berbagai pilihan permainan slot yang menarik dan inovatif, para p Kami adalah perusahaan yang menyediakan informasi lengkap tentang slot dan apa artinya. Dengan panduan kami, Anda akan dapat memahami dengan jelas konsep slot dalam berbagai konteks, mulai dari mesin
Kami adalah perusahaan yang menyediakan informasi lengkap tentang slot dan apa artinya. Dengan panduan kami, Anda akan dapat memahami dengan jelas konsep slot dalam berbagai konteks, mulai dari mesin  Admin Slot adalah platform gaming online terbaik yang menawarkan berbagai jenis permainan slot yang menarik dan mengasyikkan. Dengan fitur-fitur canggih dan antarmuka yang user-friendly, Admin Slot me
Admin Slot adalah platform gaming online terbaik yang menawarkan berbagai jenis permainan slot yang menarik dan mengasyikkan. Dengan fitur-fitur canggih dan antarmuka yang user-friendly, Admin Slot me PG Slot 888 adalah platform permainan slot online terbaik yang dapat memberikan pengalaman bermain yang seru dan menghibur bagi para penggemar slot. Dengan beragam pilihan permainan slot yang menarik
PG Slot 888 adalah platform permainan slot online terbaik yang dapat memberikan pengalaman bermain yang seru dan menghibur bagi para penggemar slot. Dengan beragam pilihan permainan slot yang menarik  Slot adalah salah satu permainan kasino paling populer di seluruh dunia. Permainan ini melibatkan pemain untuk menarik tuas atau menekan tombol guna memutar gulungan yang berisi simbol-simbol tertentu
Slot adalah salah satu permainan kasino paling populer di seluruh dunia. Permainan ini melibatkan pemain untuk menarik tuas atau menekan tombol guna memutar gulungan yang berisi simbol-simbol tertentu Kami adalah perusahaan yang menyediakan daftar slot yang memiliki banyak bonus dan memberikan kesempatan besar untuk mendapatkan jackpot. Dengan berbagai promo menarik yang kami tawarkan, Anda dapat m
Kami adalah perusahaan yang menyediakan daftar slot yang memiliki banyak bonus dan memberikan kesempatan besar untuk mendapatkan jackpot. Dengan berbagai promo menarik yang kami tawarkan, Anda dapat m Kang Toto Slot Login adalah sebuah situs agen slot online terpercaya yang menyediakan berbagai permainan slot terbaik. Dengan sistem login yang aman dan nyaman, Anda bisa menikmati beragam jenis perma
Kang Toto Slot Login adalah sebuah situs agen slot online terpercaya yang menyediakan berbagai permainan slot terbaik. Dengan sistem login yang aman dan nyaman, Anda bisa menikmati beragam jenis perma Slot 888 is a leading online casino platform that offers a wide range of exciting slot games for players to enjoy. Whether you are a seasoned pro or a casual player, our platform has something for eve
Slot 888 is a leading online casino platform that offers a wide range of exciting slot games for players to enjoy. Whether you are a seasoned pro or a casual player, our platform has something for eve Slot CQ9 merupakan salah satu permainan slot online yang banyak diminati oleh para pemain judi. Dengan tawaran fitur-fitur menarik dan jackpot besar, membuat banyak orang tertarik untuk mencoba perunt
Slot CQ9 merupakan salah satu permainan slot online yang banyak diminati oleh para pemain judi. Dengan tawaran fitur-fitur menarik dan jackpot besar, membuat banyak orang tertarik untuk mencoba perunt Main slot merupakan salah satu jenis permainan judi yang sangat populer di kalangan masyarakat. Slot sendiri adalah permainan mesin judi yang menggunakan simbol-simbol dan gulungan yang berputar. Cara
Main slot merupakan salah satu jenis permainan judi yang sangat populer di kalangan masyarakat. Slot sendiri adalah permainan mesin judi yang menggunakan simbol-simbol dan gulungan yang berputar. Cara Slot ML adalah singkatan dari Mobile Legends: Bang Bang. Slot ini merupakan tempat di dalam permainan Mobile Legends yang dapat digunakan untuk menyimpan dan mengatur berbagai item yang akan digunakan
Slot ML adalah singkatan dari Mobile Legends: Bang Bang. Slot ini merupakan tempat di dalam permainan Mobile Legends yang dapat digunakan untuk menyimpan dan mengatur berbagai item yang akan digunakan Gacoan 888 Slot adalah situs judi online terkemuka yang menyediakan berbagai macam permainan slot yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, pemain dapat dengan mudah m
Gacoan 888 Slot adalah situs judi online terkemuka yang menyediakan berbagai macam permainan slot yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, pemain dapat dengan mudah m Kami adalah perusahaan yang menyediakan berbagai macam slot yang terbukti membayar dengan kemenangan besar setiap hari. Nikmati pengalaman bermain game slot yang seru dan mengasyikkan dengan peluang k
Kami adalah perusahaan yang menyediakan berbagai macam slot yang terbukti membayar dengan kemenangan besar setiap hari. Nikmati pengalaman bermain game slot yang seru dan mengasyikkan dengan peluang k Dewa Slot 888 Login adalah salah satu situs judi slot online terpercaya yang menyediakan berbagai macam permainan slot dan casino online. Dengan tampilan yang menarik dan user-friendly, Dewa Slot 888
Dewa Slot 888 Login adalah salah satu situs judi slot online terpercaya yang menyediakan berbagai macam permainan slot dan casino online. Dengan tampilan yang menarik dan user-friendly, Dewa Slot 888  Kami adalah perusahaan pengembang permainan slot yang menyediakan berbagai pilihan slot yang bisa dimainkan secara gratis dalam mode demo. Dengan berbagai tema menarik dan fitur bonus yang menggiurkan
Kami adalah perusahaan pengembang permainan slot yang menyediakan berbagai pilihan slot yang bisa dimainkan secara gratis dalam mode demo. Dengan berbagai tema menarik dan fitur bonus yang menggiurkan Slot Gacor 888 adalah platform terkemuka yang menyediakan berbagai jenis permainan slot online yang sangat populer di kalangan pecinta judi online. Dengan koleksi slot terbaik dari provider terkemuka,
Slot Gacor 888 adalah platform terkemuka yang menyediakan berbagai jenis permainan slot online yang sangat populer di kalangan pecinta judi online. Dengan koleksi slot terbaik dari provider terkemuka, Berlian 888 Slot adalah salah satu situs judi slot online terbaik yang banyak diminati oleh para pemain. Namun, kadang-kadang terjadi kendala saat ingin login ke situs tersebut. Jika Anda mengalami ha
Berlian 888 Slot adalah salah satu situs judi slot online terbaik yang banyak diminati oleh para pemain. Namun, kadang-kadang terjadi kendala saat ingin login ke situs tersebut. Jika Anda mengalami ha Toto 888 Slot merupakan situs judi online yang menyediakan berbagai jenis permainan slot yang menarik dan seru. Dengan tampilan yang modern dan intuitif, pemain dapat dengan mudah menemukan permainan
Toto 888 Slot merupakan situs judi online yang menyediakan berbagai jenis permainan slot yang menarik dan seru. Dengan tampilan yang modern dan intuitif, pemain dapat dengan mudah menemukan permainan  Jet Slot 888 adalah sebuah perusahaan penerbangan swasta yang menyediakan layanan penerbangan jet pribadi untuk perjalanan bisnis dan liburan. Dengan armada jet mewah dan fasilitas yang modern, Jet Sl
Jet Slot 888 adalah sebuah perusahaan penerbangan swasta yang menyediakan layanan penerbangan jet pribadi untuk perjalanan bisnis dan liburan. Dengan armada jet mewah dan fasilitas yang modern, Jet Sl Kaisar 888 Slot adalah salah satu permainan slot online terbaik yang dapat dimainkan oleh para pecinta judi. Permainan ini menawarkan berbagai macam opsi permainan slot yang menarik dan seru untuk dim
Kaisar 888 Slot adalah salah satu permainan slot online terbaik yang dapat dimainkan oleh para pecinta judi. Permainan ini menawarkan berbagai macam opsi permainan slot yang menarik dan seru untuk dim Kami adalah perusahaan yang menawarkan berbagai jenis slot yang mudah jackpot (jp) bagi para penggemar judi online. Dengan bermain di platform kami, Anda memiliki kesempatan untuk memenangkan hadiah b
Kami adalah perusahaan yang menawarkan berbagai jenis slot yang mudah jackpot (jp) bagi para penggemar judi online. Dengan bermain di platform kami, Anda memiliki kesempatan untuk memenangkan hadiah b Slot Online 888 adalah tempat terbaik untuk para penggemar judi online yang ingin merasakan pengalaman bermain game casino yang menyenangkan dan mengasyikkan. Dengan berbagai pilihan permainan slot ya
Slot Online 888 adalah tempat terbaik untuk para penggemar judi online yang ingin merasakan pengalaman bermain game casino yang menyenangkan dan mengasyikkan. Dengan berbagai pilihan permainan slot ya OYO 888 Slot adalah platform judi online yang menyediakan berbagai jenis permainan slot yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, pemain dapat dengan mudah memainkan b
OYO 888 Slot adalah platform judi online yang menyediakan berbagai jenis permainan slot yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, pemain dapat dengan mudah memainkan b Titan Slot888 adalah agen slot online terpercaya yang menyediakan berbagai permainan slot yang menarik dan menghibur. Dengan sistem login yang mudah dan aman, para pemain dapat dengan nyaman mengakses
Titan Slot888 adalah agen slot online terpercaya yang menyediakan berbagai permainan slot yang menarik dan menghibur. Dengan sistem login yang mudah dan aman, para pemain dapat dengan nyaman mengakses 888 Slot adalah sebuah situs judi online terbaik yang menyediakan berbagai permainan slot yang menarik dan menghibur. Dengan link alternatif terbaru yang selalu diupdate, para pemain dapat dengan muda
888 Slot adalah sebuah situs judi online terbaik yang menyediakan berbagai permainan slot yang menarik dan menghibur. Dengan link alternatif terbaru yang selalu diupdate, para pemain dapat dengan muda Wild 888 Slot adalah situs judi online yang menawarkan berbagai macam permainan slot seru dengan tema liar dan mengasyikkan. Dengan berbagai fitur menarik seperti wild symbol, free spins, dan bonus ga
Wild 888 Slot adalah situs judi online yang menawarkan berbagai macam permainan slot seru dengan tema liar dan mengasyikkan. Dengan berbagai fitur menarik seperti wild symbol, free spins, dan bonus ga Pajak 888 Slot adalah platform judi online yang menyediakan berbagai jenis permainan slot yang menarik dan menghibur. Dengan sistem pajak yang transparan dan menguntungkan, pemain dapat menikmati berb
Pajak 888 Slot adalah platform judi online yang menyediakan berbagai jenis permainan slot yang menarik dan menghibur. Dengan sistem pajak yang transparan dan menguntungkan, pemain dapat menikmati berb Slot Finder adalah aplikasi yang dirancang khusus untuk membantu Anda menemukan makna dari 'slot' dengan mudah. Dengan fitur pencarian yang canggih, Anda dapat menemukan informasi lengkap tentang arti
Slot Finder adalah aplikasi yang dirancang khusus untuk membantu Anda menemukan makna dari 'slot' dengan mudah. Dengan fitur pencarian yang canggih, Anda dapat menemukan informasi lengkap tentang arti Slot dalam bahasa gaul dapat diartikan sebagai tempat duduk atau posisi yang tersedia untuk seseorang dalam suatu kelompok atau aktivitas. Contohnya, dalam percakapan sehari-hari, slot dapat merujuk p
Slot dalam bahasa gaul dapat diartikan sebagai tempat duduk atau posisi yang tersedia untuk seseorang dalam suatu kelompok atau aktivitas. Contohnya, dalam percakapan sehari-hari, slot dapat merujuk p Dewi 888 Slot adalah platform terbaik untuk para pecinta judi slot online. Dengan berbagai pilihan permainan slot yang menarik dan menghibur, Dewi 888 Slot menawarkan pengalaman bermain yang seru dan
Dewi 888 Slot adalah platform terbaik untuk para pecinta judi slot online. Dengan berbagai pilihan permainan slot yang menarik dan menghibur, Dewi 888 Slot menawarkan pengalaman bermain yang seru dan  Slot Berlian 888 merupakan salah satu game mesin slot yang sedang populer saat ini. Game ini menawarkan pengalaman bermain yang seru dan mengasyikkan bagi para pemainnya. Dengan desain yang menarik da
Slot Berlian 888 merupakan salah satu game mesin slot yang sedang populer saat ini. Game ini menawarkan pengalaman bermain yang seru dan mengasyikkan bagi para pemainnya. Dengan desain yang menarik da SlotLend adalah situs slot online yang memberikan kesempatan bagi para pendatang baru untuk mencoba bermain tanpa perlu mengeluarkan modal besar. Dengan fitur pinjaman saldo, pemain dapat menikmati be
SlotLend adalah situs slot online yang memberikan kesempatan bagi para pendatang baru untuk mencoba bermain tanpa perlu mengeluarkan modal besar. Dengan fitur pinjaman saldo, pemain dapat menikmati be Selamat datang di situs permainan slot terbaik di Indonesia yang selalu menghadirkan slot yang lagi gacor malam ini. Kami menawarkan berbagai macam pilihan permainan slot dengan jackpot besar yang sia
Selamat datang di situs permainan slot terbaik di Indonesia yang selalu menghadirkan slot yang lagi gacor malam ini. Kami menawarkan berbagai macam pilihan permainan slot dengan jackpot besar yang sia Tambang 888 Slot adalah situs judi online yang menyediakan berbagai macam permainan slot dengan keuntungan besar. Dengan tampilan yang menarik dan mudah digunakan, para pemain dapat dengan mudah menik
Tambang 888 Slot adalah situs judi online yang menyediakan berbagai macam permainan slot dengan keuntungan besar. Dengan tampilan yang menarik dan mudah digunakan, para pemain dapat dengan mudah menik Slot Judi 888 adalah situs judi online terpercaya yang menyediakan beragam permainan slot dengan kualitas premium. Dengan tampilan yang modern dan fitur-fitur terbaik, pemain dapat merasakan sensasi b
Slot Judi 888 adalah situs judi online terpercaya yang menyediakan beragam permainan slot dengan kualitas premium. Dengan tampilan yang modern dan fitur-fitur terbaik, pemain dapat merasakan sensasi b XYZ 888 Slot merupakan salah satu permainan slot online yang sedang populer saat ini. Dengan berbagai fitur dan bonus yang menarik, pemain memiliki kesempatan untuk memenangkan jackpot besar. Dengan t
XYZ 888 Slot merupakan salah satu permainan slot online yang sedang populer saat ini. Dengan berbagai fitur dan bonus yang menarik, pemain memiliki kesempatan untuk memenangkan jackpot besar. Dengan t Ratu Slot 888 Login adalah platform perjudian online terkemuka yang menawarkan berbagai macam permainan slot yang menarik dan menghibur. Dengan sistem login yang mudah dan aman, para pemain dapat deng
Ratu Slot 888 Login adalah platform perjudian online terkemuka yang menawarkan berbagai macam permainan slot yang menarik dan menghibur. Dengan sistem login yang mudah dan aman, para pemain dapat deng Slot 888 adalah platform terbaik untuk para pecinta judi slot online. Dengan berbagai pilihan permainan slot yang menarik dan menghibur, Anda akan dapat menikmati pengalaman bermain yang seru dan meng
Slot 888 adalah platform terbaik untuk para pecinta judi slot online. Dengan berbagai pilihan permainan slot yang menarik dan menghibur, Anda akan dapat menikmati pengalaman bermain yang seru dan meng Kaisar 888 Slot adalah platform permainan slot online terbaik yang dirancang khusus untuk para pecinta judi. Dengan berbagai pilihan permainan slot yang menarik dan seru, pemain dapat menikmati pengal
Kaisar 888 Slot adalah platform permainan slot online terbaik yang dirancang khusus untuk para pecinta judi. Dengan berbagai pilihan permainan slot yang menarik dan seru, pemain dapat menikmati pengal Permainan slot merupakan salah satu permainan judi yang sangat populer di kalangan pecinta judi online. Slot memiliki daya tarik tersendiri karena sangat mudah dimainkan dan memberikan kesempatan untu
Permainan slot merupakan salah satu permainan judi yang sangat populer di kalangan pecinta judi online. Slot memiliki daya tarik tersendiri karena sangat mudah dimainkan dan memberikan kesempatan untu Situs slot pulsa Indosat adalah tempat terbaik bagi Anda yang ingin menikmati berbagai jenis permainan slot online dengan kemudahan melakukan deposit melalui pulsa Indosat. Dengan berbagai pilihan per
Situs slot pulsa Indosat adalah tempat terbaik bagi Anda yang ingin menikmati berbagai jenis permainan slot online dengan kemudahan melakukan deposit melalui pulsa Indosat. Dengan berbagai pilihan per Kami adalah perusahaan yang menawarkan berbagai macam permainan slot dari provider CQ9 yang terkenal dengan keberuntungan tinggi. Dengan berbagai fitur menarik dan tata letak yang mudah dipahami, Anda
Kami adalah perusahaan yang menawarkan berbagai macam permainan slot dari provider CQ9 yang terkenal dengan keberuntungan tinggi. Dengan berbagai fitur menarik dan tata letak yang mudah dipahami, Anda PG Slot 888 adalah platform terkemuka yang menyediakan berbagai permainan slot online yang menarik dan menghibur. Dengan koleksi permainan yang beragam dan kualitas grafis yang tinggi, PG Slot 888 men
PG Slot 888 adalah platform terkemuka yang menyediakan berbagai permainan slot online yang menarik dan menghibur. Dengan koleksi permainan yang beragam dan kualitas grafis yang tinggi, PG Slot 888 men SlotMania adalah situs slot online terbaik yang menyediakan berbagai permainan slot menarik dan menghibur. Dengan sistem pembayaran yang fleksibel, Anda dapat melakukan deposit menggunakan pulsa Indos
SlotMania adalah situs slot online terbaik yang menyediakan berbagai permainan slot menarik dan menghibur. Dengan sistem pembayaran yang fleksibel, Anda dapat melakukan deposit menggunakan pulsa Indos Jet Slot 888 merupakan salah satu jenis mesin slot online yang populer di kalangan para pemain judi online. Mesin slot ini memiliki berbagai fitur menarik dan grafis yang memukau, sehingga menarik min
Jet Slot 888 merupakan salah satu jenis mesin slot online yang populer di kalangan para pemain judi online. Mesin slot ini memiliki berbagai fitur menarik dan grafis yang memukau, sehingga menarik min Judi slot 888 online merupakan salah satu jenis permainan judi yang paling populer saat ini. Dengan banyaknya pilihan permainan dan kemungkinan untuk meraih kemenangan besar, tidak mengherankan jika b
Judi slot 888 online merupakan salah satu jenis permainan judi yang paling populer saat ini. Dengan banyaknya pilihan permainan dan kemungkinan untuk meraih kemenangan besar, tidak mengherankan jika b Anak Slot888 adalah situs judi online terkemuka yang menyediakan berbagai permainan slot terbaik untuk para pecinta judi. Dengan tampilan yang menarik dan fitur yang lengkap, Anak Slot888 menjadi pili
Anak Slot888 adalah situs judi online terkemuka yang menyediakan berbagai permainan slot terbaik untuk para pecinta judi. Dengan tampilan yang menarik dan fitur yang lengkap, Anak Slot888 menjadi pili Besar 888 Slot adalah salah satu platform judi online yang sedang populer saat ini. Platform ini menawarkan berbagai macam permainan slot yang menarik dan seru untuk dimainkan. Bermain di Besar 888 Sl
Besar 888 Slot adalah salah satu platform judi online yang sedang populer saat ini. Platform ini menawarkan berbagai macam permainan slot yang menarik dan seru untuk dimainkan. Bermain di Besar 888 Sl Kami adalah perusahaan yang menyediakan platform permainan slot online yang memungkinkan para pemain untuk melakukan deposit menggunakan uang asli. Dengan sistem pembayaran yang terjamin keamanannya,
Kami adalah perusahaan yang menyediakan platform permainan slot online yang memungkinkan para pemain untuk melakukan deposit menggunakan uang asli. Dengan sistem pembayaran yang terjamin keamanannya,  Saat ini, semakin banyak situs slot online yang menyediakan metode pembayaran dengan deposit pulsa Indosat. Hal ini tentu saja memudahkan para pemain yang tidak memiliki rekening bank untuk melakukan
Saat ini, semakin banyak situs slot online yang menyediakan metode pembayaran dengan deposit pulsa Indosat. Hal ini tentu saja memudahkan para pemain yang tidak memiliki rekening bank untuk melakukan  Turnover dalam slot adalah istilah yang sering digunakan dalam dunia perjudian online. Turnover mengacu pada jumlah total uang yang dipertaruhkan oleh pemain dalam periode waktu tertentu. Dalam kontek
Turnover dalam slot adalah istilah yang sering digunakan dalam dunia perjudian online. Turnover mengacu pada jumlah total uang yang dipertaruhkan oleh pemain dalam periode waktu tertentu. Dalam kontek Berlian Slot 888 adalah agen judi slot online terpercaya yang menyediakan berbagai macam permainan slot dengan kualitas terbaik. Dengan sistem keamanan yang tinggi, para pemain dapat bermain dengan ny
Berlian Slot 888 adalah agen judi slot online terpercaya yang menyediakan berbagai macam permainan slot dengan kualitas terbaik. Dengan sistem keamanan yang tinggi, para pemain dapat bermain dengan ny Seiring dengan perkembangan teknologi yang semakin pesat, kini bermain slot online semakin menyenangkan dan mudah. Salah satu kemudahan yang ditawarkan oleh situs slot online adalah kemampuan untuk me
Seiring dengan perkembangan teknologi yang semakin pesat, kini bermain slot online semakin menyenangkan dan mudah. Salah satu kemudahan yang ditawarkan oleh situs slot online adalah kemampuan untuk me Koin slot 888 adalah salah satu jenis permainan judi online yang sangat populer saat ini. Dengan tampilan yang menarik dan sistem permainan yang mudah dipahami, membuat koin slot 888 menjadi pilihan f
Koin slot 888 adalah salah satu jenis permainan judi online yang sangat populer saat ini. Dengan tampilan yang menarik dan sistem permainan yang mudah dipahami, membuat koin slot 888 menjadi pilihan f Rajanya Slot adalah situs perjudian online yang menyediakan berbagai pilihan permainan slot terbaik di Indonesia. Dikenal sebagai situs slot terbesar di Indonesia, Rajanya Slot menawarkan berbagai mac
Rajanya Slot adalah situs perjudian online yang menyediakan berbagai pilihan permainan slot terbaik di Indonesia. Dikenal sebagai situs slot terbesar di Indonesia, Rajanya Slot menawarkan berbagai mac No Limit City adalah penyedia slot terkemuka yang telah hadir dalam industri perjudian online selama bertahun-tahun. Mereka dikenal dengan berbagai fitur menarik yang mereka tawarkan, termasuk desain
No Limit City adalah penyedia slot terkemuka yang telah hadir dalam industri perjudian online selama bertahun-tahun. Mereka dikenal dengan berbagai fitur menarik yang mereka tawarkan, termasuk desain  Situs judi slot 888 merupakan salah satu tempat terbaik untuk bermain game slot online. Dengan berbagai permainan yang menarik dan menghibur, situs ini menawarkan pengalaman bermain yang seru dan meng
Situs judi slot 888 merupakan salah satu tempat terbaik untuk bermain game slot online. Dengan berbagai permainan yang menarik dan menghibur, situs ini menawarkan pengalaman bermain yang seru dan meng Tambang Slot 888 adalah situs perjudian online terbaik yang menawarkan berbagai permainan slot yang menarik dan menghibur. Dengan koleksi game yang lengkap dan grafis yang memukau, Anda pasti akan men
Tambang Slot 888 adalah situs perjudian online terbaik yang menawarkan berbagai permainan slot yang menarik dan menghibur. Dengan koleksi game yang lengkap dan grafis yang memukau, Anda pasti akan men XL Slot 888 adalah salah satu agen judi slot online terpercaya yang menyediakan berbagai jenis permainan slot terbaik. Dengan sistem yang fair play dan transaksi yang mudah, XL Slot 888 menjadi piliha
XL Slot 888 adalah salah satu agen judi slot online terpercaya yang menyediakan berbagai jenis permainan slot terbaik. Dengan sistem yang fair play dan transaksi yang mudah, XL Slot 888 menjadi piliha dalam Slot dan Bagaimana Cara Menghitungnya?.webp) TO atau Turnover dalam slot online adalah jumlah total taruhan yang dipasang oleh pemain dalam periode waktu tertentu. TO biasanya digunakan oleh situs slot online untuk menghitung berbagai bonus dan
TO atau Turnover dalam slot online adalah jumlah total taruhan yang dipasang oleh pemain dalam periode waktu tertentu. TO biasanya digunakan oleh situs slot online untuk menghitung berbagai bonus dan  Situs slot yang terpercaya merupakan tempat yang aman dan nyaman untuk para penggemar permainan slot online. Dengan banyaknya situs slot yang bermunculan saat ini, penting bagi para pemain untuk bisa
Situs slot yang terpercaya merupakan tempat yang aman dan nyaman untuk para penggemar permainan slot online. Dengan banyaknya situs slot yang bermunculan saat ini, penting bagi para pemain untuk bisa  Kami adalah situs judi online terbaik yang menawarkan berbagai jenis permainan slot gacor yang pasti membuat Anda ketagihan. Apa itu slot gacor? Slot gacor merupakan slot online yang memiliki tingkat
Kami adalah situs judi online terbaik yang menawarkan berbagai jenis permainan slot gacor yang pasti membuat Anda ketagihan. Apa itu slot gacor? Slot gacor merupakan slot online yang memiliki tingkat  Slot Resmi 888 adalah platform terpercaya yang menyediakan berbagai jenis permainan slot online untuk para penggemar judi. Dengan lisensi resmi dari otoritas perjudian internasional, Anda dapat yakin
Slot Resmi 888 adalah platform terpercaya yang menyediakan berbagai jenis permainan slot online untuk para penggemar judi. Dengan lisensi resmi dari otoritas perjudian internasional, Anda dapat yakin  Kami adalah perusahaan yang menyediakan berbagai macam pilihan slot online dengan tingkat pengembalian (RTP) tertinggi. Dengan beragam tema dan fitur menarik, setiap pemain dapat menemukan permainan y
Kami adalah perusahaan yang menyediakan berbagai macam pilihan slot online dengan tingkat pengembalian (RTP) tertinggi. Dengan beragam tema dan fitur menarik, setiap pemain dapat menemukan permainan y Togel Slot 888 merupakan salah satu situs judi online terbaik yang menyediakan berbagai permainan slot yang menarik. Dengan berbagai pilihan permainan slot yang bisa dimainkan, para pemain dapat menik
Togel Slot 888 merupakan salah satu situs judi online terbaik yang menyediakan berbagai permainan slot yang menarik. Dengan berbagai pilihan permainan slot yang bisa dimainkan, para pemain dapat menik Kaisar 888 merupakan platform judi online terpercaya yang menyediakan beragam permainan slot yang menarik dan menghibur. Dengan sistem login yang mudah dan cepat, para penggemar slot dapat dengan nyam
Kaisar 888 merupakan platform judi online terpercaya yang menyediakan beragam permainan slot yang menarik dan menghibur. Dengan sistem login yang mudah dan cepat, para penggemar slot dapat dengan nyam Selamat datang di situs judi slot 888 terbaik di Indonesia! Kami menyediakan berbagai jenis permainan slot online yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, Anda akan m
Selamat datang di situs judi slot 888 terbaik di Indonesia! Kami menyediakan berbagai jenis permainan slot online yang menarik dan menghibur. Dengan tampilan yang modern dan user-friendly, Anda akan m